Network Security Basics
1. Authentication & Encryption
-
Authentication verifies identity using credentials like passwords, tokens, multi-factor authentication, or certificates
-
Encryption protects data in transit and at rest via algorithms:
-
Symmetric (e.g., AES): uses one secret key.
-
Asymmetric (e.g., RSA/ECC): uses public/private key pairs—ideal for secure key exchange .
-
-
Hybrid cryptosystems utilize asymmetric encryption to securely exchange symmetric session keys (e.g., TLS/SSL) en.wikipedia.org.
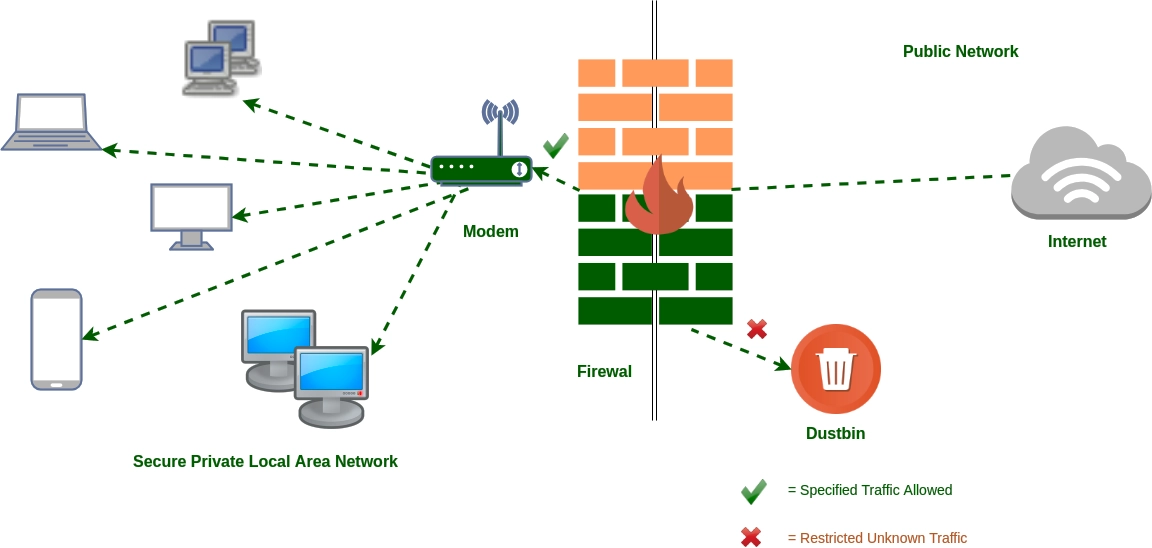
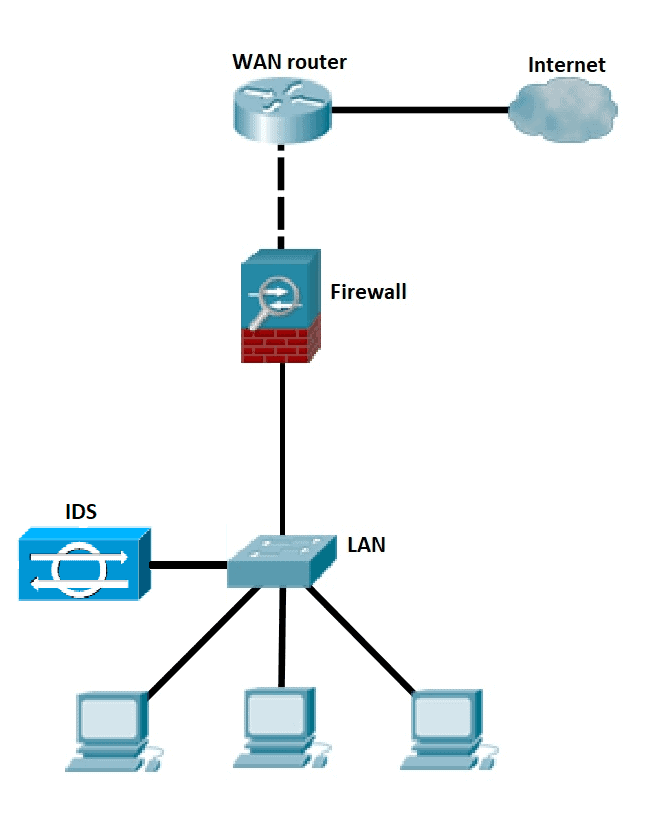
Firewalls & Intrusion Detection/Prevention
-
Firewalls control access based on predefined rules:
-
Types: Packet‑filtering, Stateful Inspection, Next‑Gen Firewalls (NGFW)
-
They monitor traffic between zones (e.g., LAN ↔ WAN), deciding to allow or block flows safeaeon.com.
-
Diagram shows how the firewall sits at the network perimeter, filtering traffic between internal and external networks.
-
-
Intrusion Detection Systems (IDS):
-
Monitor and alert but do not block malicious activity.
-
Types:
-
Signature-based – match known attack patterns.
-
Anomaly-based – flag unusual behavior network-insight.net+14aryanstha.medium.com+14developnsolve.com+14en.wikipedia.org.
-
-
-
Intrusion Prevention Systems (IPS):
-
Are inline, capable of blocking detected threats
-
May reconfigure firewalls or drop malicious packets

-
. 
 Virtual Private Networks (VPNs)
Virtual Private Networks (VPNs)
-
A VPN creates a secure, encrypted tunnel over untrusted public networks, protecting confidentiality and integrity
-
Modes:
-
Remote-access: end-user device connects to private network.
-
Site-to-site: connects two networks (e.g., branch office
-
-
Security features include:
-
Encryption to prevent eavesdropping.
-
Authentication of endpoints via credentials or certificates.
-
Data integrity blocking altered or replayed packets
-
-
Diagram illustrates client → encrypted VPN tunnel → corporate network

Table
| Component | Purpose |
|---|---|
| Authentication | Verify user/device identity before granting access fynd.academy |
| Encryption | Secure confidentiality and integrity |
| Firewalls | Filter traffic based on rules, zones, apps |
| IDS / IPS | Detect anomalies and prevent attacks |
| VPNs | Securely extend private networks over public internet |

